Research into automotive cyber security: server and digital key are the ports vulnerable to attacks, for which OEMs have stepped up efforts in cyber security.
With advances in the CASE (Connected, Autonomous, Shared, and Electrified) trend, cars are going smarter ever with functional enrichment. Statistically, the installation rate of telematics feature to new cars in China is over 50% from January to October of 2020, a figure projected to rise to 75% or so in 2025. In terms of functionality, intelligent cockpit and advanced automated driving become trending, and the features such as multi-modal interaction, multi-display interaction, 5G connectivity, V2X, OTA and digital key finds ever broader application alongside the soaring number of vehicle control codes and more port vulnerabilities to safety threat.
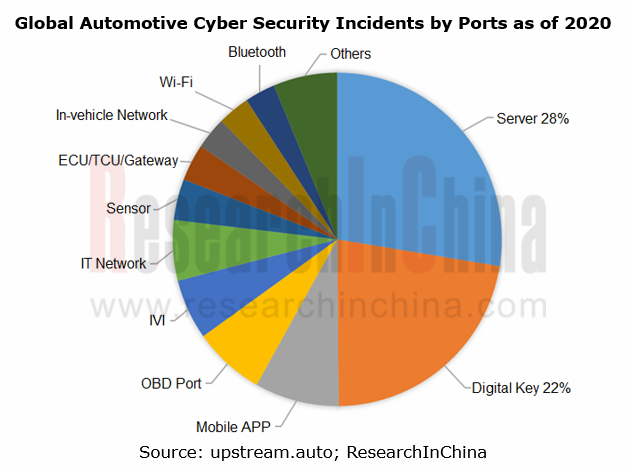
Currently, the automotive cyber security events arise mainly from attacks on server, digital key, mobile APP, OBD port among others.
Server acts as the most important port for cyber security, which is exposed to the attack by hackers on operating system, database, TSP server, OTA server and the like, thus issuing in data tampering, damage and vehicle safety accidents. Most tools of assault on servers are remotely accessible with lower costs, while the data storage over servers is of paramount importance, all of which lead to often a rather high share of attacks on servers.
Digital key, as the second port that matters most to cyber security, is a common media subject to vehicle intrusion and theft. In 2020, there will be 300,000 Bluetooth digital key installs in China, coupled with an installation rate at about 4%, with such more functionalities besides lock/unlock & start as account log-in, key sharing, vehicle trajectory record, and parcel delivery to cars, which has ever more implications on vehicle safety.
Different auto brands are subject to varied attack on vehicle security.
The smarter a car is, the more vulnerable to security attacks will be. Amid the intelligence trend, all OEMs, whatever Mercedes-Benz, BMW, Audi, VW, Toyota, Honda or Hyundai, have varied exposure to security attacks.
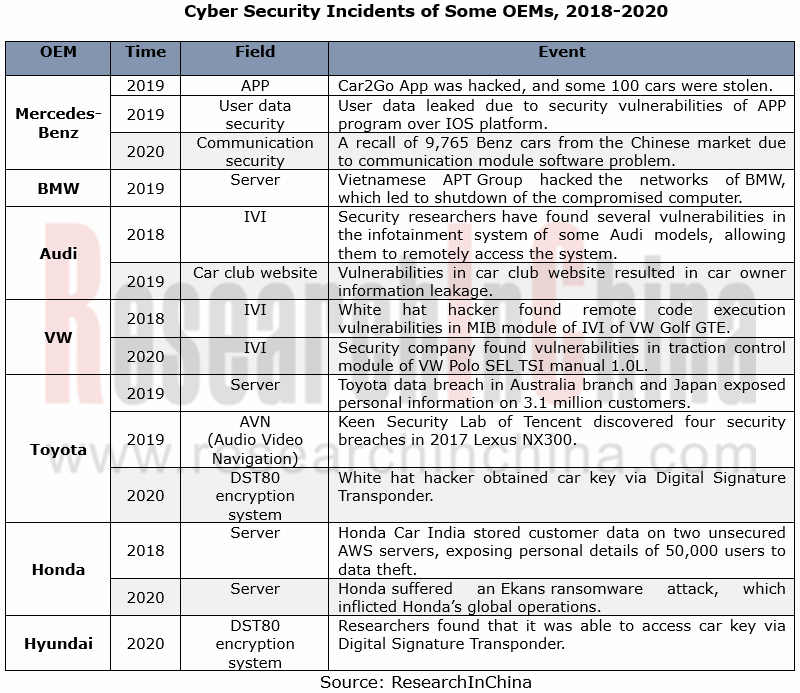
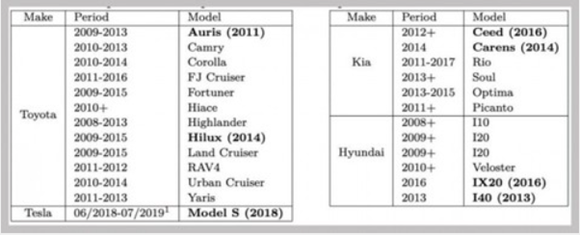
In March 2020, key encryption approaches of OEMs like Toyota, Hyundai and KIA were reported to have limitations with a possibility of intrusions and thefts largely due to the vulnerabilities of TI’s DST80 encryption system employed by them. A hacker just stands near the car that packs DST80 remote control key, using the inexpensive Proxmark RFID reader/transmitter for the ‘identity theft’ of the key and thus getting the encrypted information.
OEM quicken their presence in cyber security
To address serious challenges in automotive cyber security, the OEMs are sparing no efforts in security improvement in many aspects: a) information management inside the company and optimization of R&D process; 2) to build a team intended for cyber security; 3) cyber security protection of telematics.
> European and American OEMs: Diversified deployments of cyber security protection
The automakers from Europe and America are pushing ahead with cyber security construction roundly with technical superiorities, with a tightened control on information security management inside the company apart from improvements in cyber security protection of telematics. As concerns team construction, the majority of European and American OEMs as usual set up either an independent cyber security division or a subsidiary to ensure information security during a vehicle lifespan.
Mercedes-Benz, for instance, has such actions for cyber security in the three below:
Cloud computing: vehicle data protection enabled by a cloud platform through which the car owner takes control of data openness to the outside while driving, and at the same time relevant information will be eliminated automatically after the car owner leaves his/her car;
Factory: partnership with telecom carriers and equipment vendors to set up intelligent vehicle manufacturing factories with production data safety enabled by 5G mobile network;
Vulnerability protection: joins forces with third-party cybersecurity providers to test and repair the potential vulnerabilities of intelligent connected vehicle.
> Japanese and Korean OEMs: with a more focus on cyber security protection and management inside the company
Nissan Motor, for example, proceeds with intro-company management on information security and perfects the regulations concerned. Over the recent years, Nissan has been improving its R&D management system and cyber security platform, with its Tel Aviv-based joint innovation laboratory and collaborations with Israeli start-ups on cyber security testing and study. As yet, Nissan has more than ten cooperative joint prototype projects.
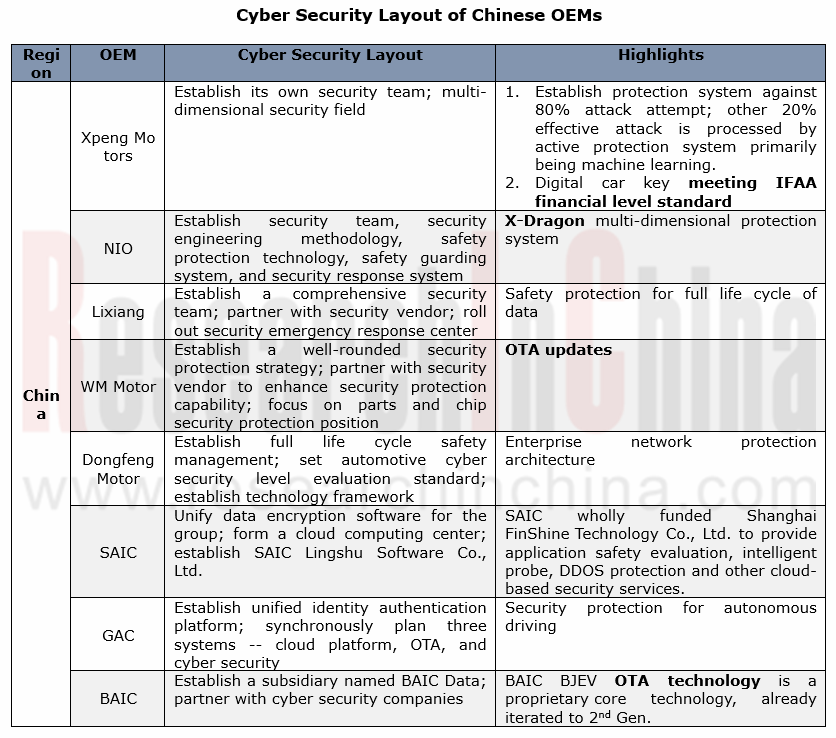
> Chinese OEMs: the emerging forces go ahead of the rest
The emerging carmakers are commendable in cyber security protection. Cases include XPENG Motors that boast concurrent deployments over cloud, vehicle and mobile phone by building a security team on its own and the partnerships with Aliyun, Irdeto, and Keen Security Lab of Tencent in order for a proactive protection system; and NIO that has built a X-Dragon multi-dimensional protection system through a self-owned security team and multi-party cooperation.
Also, the time-honored Chinese automakers follow suit, such as Dongfeng Motor, SAIC, GAC and BAIC that all prioritize the security stewardship during their life cycle. As concerns its overall deployment, SAIC, for example, incorporates its subordinates into the group’s cyber security protection and management system and applies the data encryption software (GS-EDS system) with one accord for data safety as a whole; secondly, SAIC builds a cloud platform independently and a proprietary cloud computing center delivering cloud-based security services; last, SAIC founded SAIC Lingshu Software Co., Ltd in charge of developing basic technology platform and sharpening software R&D competence.
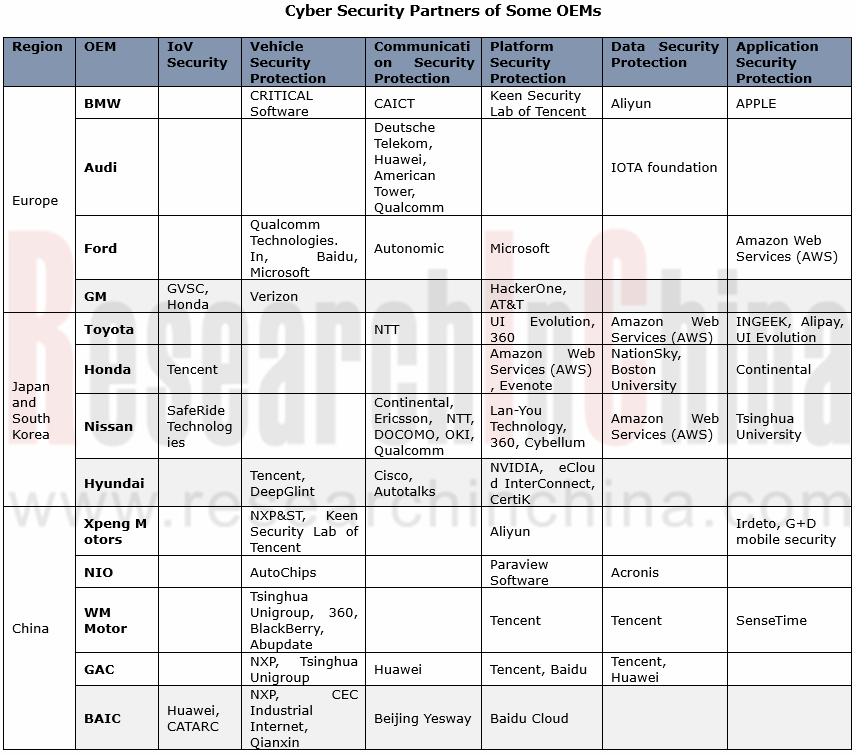
OEMs have ever broader cooperation in cyber security.
In addition to security enhancement, OEMs are vigorously seeking for external collaborations on vehicle, communication, platform, data, and application, to name a few.
Automotive Digital Key Industry Trend Report, 2026
Digital Key Research: Automotive BLE, UWB and SLE Hardware Layout
The Automotive Digital Key Industry Trend Report, 2026, released by ResearchInChina, analyzes and predicts the digital key market, co...
Monthly Report on Automotive New Technology (May 2026)
UHD gaze technology, full-color LiDAR, UWB, etc. promote the upgrade of intelligent driving perception capabilities
This report is published once a month and is available for annual subscription.The...
In-Cabin Monitoring Systems (DMS, OMS, etc.) Research Report, 2026
In-Cabin Monitoring System Research: DMS to Become Mandatory in 2027, Expected to be Installed in Over 14 Million Vehicles
ResearchInChina released the In-Cabin Monitoring Systems (DMS, OMS, etc.) Re...
Automotive Service-Oriented Architecture (SOA) and Cross-Domain Middleware Industry Report, 2026
Research on automotive SOA and cross-domain middleware: The era of AI atomic services and AI cross-domain fusion agents is coming.
Automotive SOA evolves towards AI + full SOA servitization Driv...
Automotive Display, Center Console and Cluster Industry Report, 2026
Automotive Display Research: Multi-Screen Application Slows Down, While OLED and MiniLED Are Introduced in Vehicles Quickly
In 2026, automotive displays will no longer excessively pursue the number a...
Global and China Intelligent Vehicle Standard System Construction and Certification Research Report, 2026
Intelligent Driving Standards and Certification: With the Maturing Standardization System, China Will Participate in Formulation of Global Standards
China's automotive industry is transforming from ...
Automotive Intelligent Diagnosis Industry Report, 2026
Automotive Intelligent Diagnosis Research: Powered by AI, Remote Diagnosis Is Being Upgraded towards Intelligence.
ResearchInChina released the Automotive Intelligent Diagnosis Industry Report, 2026....
Automotive Cloud Service Platform Research Report, 2026
Research on automotive cloud service platform: with architecture upgrade and computing power improvement, cloud services enter a new stage
In 2026, the Internet of Vehicles industry generates petaby...
Integrated Battery and Innovative Battery Technology Research Report, 2026
Power Battery Research: Sales of High-Capacity Vehicles Keep Rising, and Solid-State Batteries Begin to Be Installed in Vehicles
I. Sales of High-Capacity Vehicles Sustain Growth, and Those with A C...
Chinese Independent OEMs’ ADAS and Autonomous Driving Report, 2026
Research on OEMs' Intelligent Driving: Era of Physical AI, Standard Configuration of D2D, and Initial Exploration of L3 Commercial Pilot Projects
From 2023 to 2025, the intelligent driving installati...
Intelligent Vehicle New Technology Application Analysis Report, 2025-2026
New Technology Research: Innovative Products such as Bionic Cameras, Vision-LiDAR Fusion Sensors, Auditory Sensors Further Enhance Vehicle Perception Capabilities
ForewordResearchInChina released th...
Automotive Optical Fiber Communication (Optical Fiber Ethernet, PON) and Supply Chain Research Report, 2026
Research on Automotive Optical Fiber Communication: Introduction of Optical Fiber in Vehicles Accelerates, with Priority Deployment in High-Speed Communication Link (10+Gbps) Scenarios
Automotive opt...
Automotive Intelligent Cockpit SoC Research Report, 2026
Automotive Cockpit SoC Research: Passenger Cars in the Price Range of RMB100,000–200,000 Account for Nearly 50% of Total Sales, and New-Generation Cockpit SoC Products Largely Enter Mass Production
P...
LiDAR (Automotive, Pan-Robotics, etc.) Application Research Report, 2025-2026
LiDAR research: hardware competition shifts to combined sensing capabilities from "point cloud" to "images” and from automotive to robots The "LiDAR (Automotive, Pan-Robotics, ...
Global and China Passenger Car T-Box Market Report, 2026
Based on 2025 market data and the latest business layouts of OEMs and suppliers from 2025 to 2026, this report analyzes the development status quo and future trends of China’s passenger car T-Box mark...
Global and China Range Extended Electric Vehicle (REEV) and Plug-in Hybrid Electric Vehicle (PHEV) Research Report, 2026
Research on REEVs and PHEVs: Foreign OEMs are considering extended-range technology as an important strategic option and will launch a series of new vehicles
Global PHEVs & REEVs tend to be domin...
Automotive Voice Industry Report, 2026
Automotive Voice Research: Explosive Growth in Features Like "See and Speak", 35-Fold Increase in External Voice Interaction in Two Years
ResearchInChina has released the Automotive Voice Industry R...
China Passenger Car Digital Chassis Research Report, 2026
Research on Digital Chassis: Leading OEMs Have Completed Configuration of Version 2.0 1. Leading OEMs Have Completed Configuration of Digital Chassis 2.0
By the degree of wired control of each c...